springsecurity自定义userService和认证逻辑(在springboot中)_userservice instanceof springsecurityuserservice-程序员宅基地
技术标签: Java spring boot java spring security
看了一下感觉这东西还挺难的,得写点什么来总结一下。
1.要启用springsecurity很简单只需要在pom.xml中添加相关依赖就行了
<dependency>
<groupId>org.springframework.boot</groudId>
<artifactId>spring-boot-starter-security</artifactId>
</dependency>
2.准备User类和Role类,这里直接用JPA
@Entity(name = "t_user")
public class User implements UserDetails {
@Id
@GeneratedValue(strategy = GenerationType.IDENTITY)
private Long id;
private String username;
private String password;
private boolean accountNonExpired;
private boolean accountNonLocked;
private boolean credentialsNonExpired;
private boolean enabled;
@ManyToMany(fetch = FetchType.EAGER,cascade = CascadeType.PERSIST)
private List<Role> roles;
@Override
public Collection<? extends GrantedAuthority> getAuthorities() {
List<SimpleGrantedAuthority> authorities = new ArrayList<>();
for(Role role:getRoles()){
authorities.add(new SimpleGrantedAuthority(role.getName()));
}
return authorities;
}
@Override
public String getPassword() {
return password;
}
@Override
public String getUsername() {
return username;
}
@Override
public boolean isAccountNonExpired() {
return accountNonExpired;
}
@Override
public boolean isAccountNonLocked() {
return accountNonLocked;
}
@Override
public boolean isCredentialsNonExpired() {
return credentialsNonExpired;
}
@Override
public boolean isEnabled() {
return enabled;
}
//下面是基本的getter和setter
public Long getId() {
return id;
}
public void setId(Long id) {
this.id = id;
}
public void setUsername(String username) {
this.username = username;
}
public void setPassword(String password) {
this.password = password;
}
public void setAccountNonExpired(boolean accountNonExpired) {
this.accountNonExpired = accountNonExpired;
}
public void setAccountNonLocked(boolean accountNonLocked) {
this.accountNonLocked = accountNonLocked;
}
public void setCredentialsNonExpired(boolean credentialsNonExpired) {
this.credentialsNonExpired = credentialsNonExpired;
}
public void setEnabled(boolean enabled) {
this.enabled = enabled;
}
public List<Role> getRoles() {
return roles;
}
public void setRoles(List<Role> roles) {
this.roles = roles;
}
}
用户实体类主要需要实现 UserDetails 接口,并实现接口中的方法。
这里的字段基本都好理解,几个特殊的我来稍微说一下:
accountNonExpired、accountNonLocked、credentialsNonExpired、enabled 这四个属性分别用来描述用户的状态,表示账户是否没有过期、账户是否没有被锁定、密码是否没有过期、以及账户是否可用。
roles 属性表示用户的角色,User 和 Role 是多对多关系,用一个 @ManyToMany 注解来描述。
getAuthorities 方法返回用户的角色信息,我们在这个方法中把自己的 Role 稍微转化一下即可。
3.定义UserDao和UserService
public interface UserDao extends JpaRepository<User,Long> {
User findUserByUsername(String username);
}
@Service
public class UserService implements UserDetailsService {
@Autowired
UserDao userDao;
@Override
public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException {
User user = userDao.findUserByUsername(username);
if(user==null){
throw new UsernameNotFoundException("用户不存在");
}
return user;
}
}
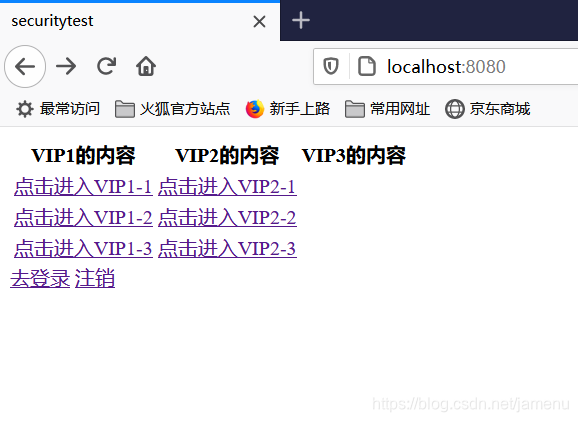
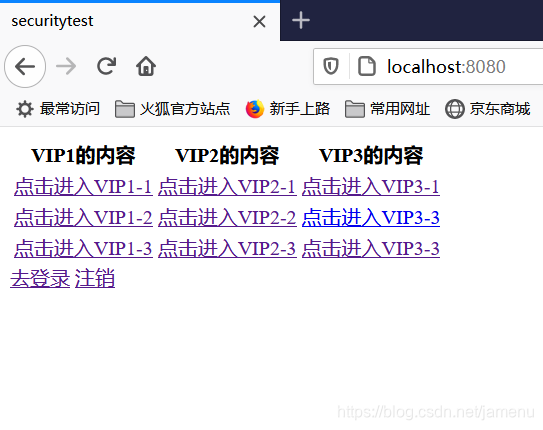
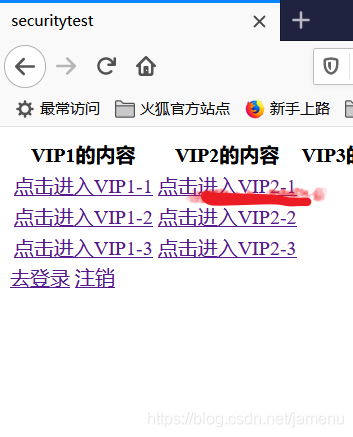
4.前端定义了一组页面,分别划归3个不同得权限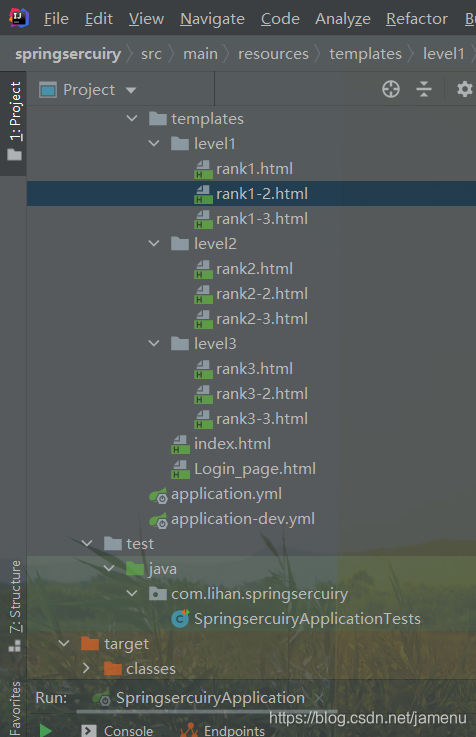
在首页中写了个table并放上三类页面的超链接
<!DOCTYPE html>
<html lang="en" xmlns:th="http://www.thymeleaf.org"
xmlns:sec="http://www.thymeleaf.org/thymeleaf-extras-springsecurity5">
<head>
<meta charset="UTF-8">
<title>securitytest</title>
</head>
<body>
<table>
<thead>
<tr>
<th>VIP1的内容</th>
<th>VIP2的内容</th>
<th>VIP3的内容</th>
</tr>
</thead>
<tbody>
<tr>
<td><a th:href="@{/level1/rank1}">点击进入VIP1-1</a></td>
<td><a th:href="@{/level2/rank2}">点击进入VIP2-1</a></td>
<div sec:authorize="hasRole('ROLE_vip3')"> <td><a th:href="@{/level3/rank3}">点击进入VIP3-1</a></td> </div>
</tr>
<tr>
<td><a th:href="@{/level1/rank1-2}">点击进入VIP1-2</a></td>
<td><a th:href="@{/level2/rank2-2}">点击进入VIP2-2</a></td>
<div sec:authorize="hasRole('ROLE_vip3')"><td><a th:href="@{/level3/rank3-2}">点击进入VIP3-3</a></td></div>
</tr>
<tr>
<td><a th:href="@{/level1/rank1-3}">点击进入VIP1-3</a></td>
<td><a th:href="@{/level2/rank2-3}">点击进入VIP2-3</a></td>
<div sec:authorize="hasRole('ROLE_vip3')"><td><a th:href="@{/level3/rank3-3}">点击进入VIP3-3</a></td></div>
</tr>
</tbody>
</table>
<a th:href="@{/Login_page}">去登录</a>
<a th:href="@{/logout}">注销</a>
</body>
</html>
(PS)要使用thymeleaf和springsecurity的整合需要在pom.xml中添加如下依赖
<dependency>
<groupId>org.thymeleaf.extras</groupId>
<artifactId>thymeleaf-extras-springsecurity5</artifactId>
<version>3.0.4.RELEASE</version>
</dependency>
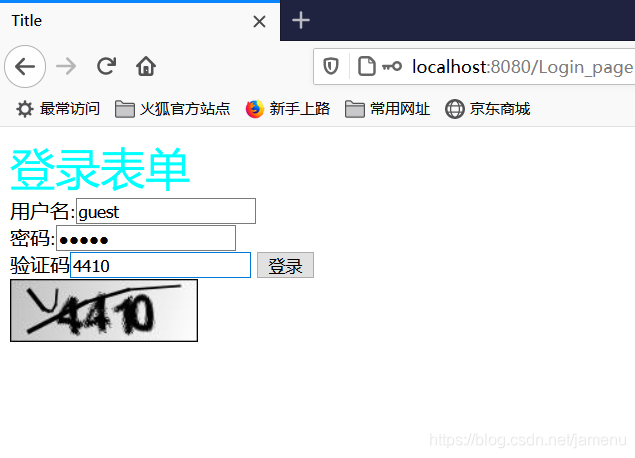
登录页面可以是springsecurity提供的,也可以是自己写的,这里自己写一个简单的登录页面Login_page.html
<body>
<form th:action="@{/Login_page}" method="post">
<span style="color: aqua;font-size: 36px;text-align: center">登录表单</span><br>
<label>用户名:</label><input type="text" name="username" /><br>
<label>密码:</label><input type="password" name="password"/><br>
<input type="submit" value="登录"/>
</form>
之后写一个Controller去跳转这些页面
controller
@Controller
public class LoginController {
@RequestMapping({
"/","/index","/index.html"})
public String toindex(){
return "index";
}
@RequestMapping("/Login_page")
public String toLogin(){
return "Login_page";
}
@RequestMapping({
"/level1/rank1","/level1/rank1.html"})
public String level1rank1(){
return "level1/rank1";
}
@RequestMapping({
"/level1/rank1-2","/level1/rank1-2.html"})
public String level1rank2(){
return "level1/rank1-2";
}
@RequestMapping({
"/level1/rank1-3","/level1/rank1-3.html"})
public String level1rank3(){
return "level1/rank1-3";
}
@RequestMapping({
"/level2/rank2","/level2/rank2.html"})
public String level2rank1(){
return "level2/rank2";
}
@RequestMapping({
"/level2/rank2-2","/level2/rank2-2.html"})
public String level2rank2(){
return "level2/rank2-2";
}
@RequestMapping({
"/level2/rank2-3","/level2/rank2-3.html"})
public String level2rank3(){
return "level2/rank2-3";
}
///
@RequestMapping({
"/level3/rank3","/level3/rank3.html"})
public String level3rank1(){
return "level3/rank3";
}
@RequestMapping({
"/level3/rank3-2","/level3/rank3-2.html"})
public String level3rank2(){
return "level3/rank3-2";
}
@RequestMapping({
"/level3/rank3-3","/level3/rank3-3.html"})
public String level3rank3(){
return "level3/rank3-3";
}
//
}
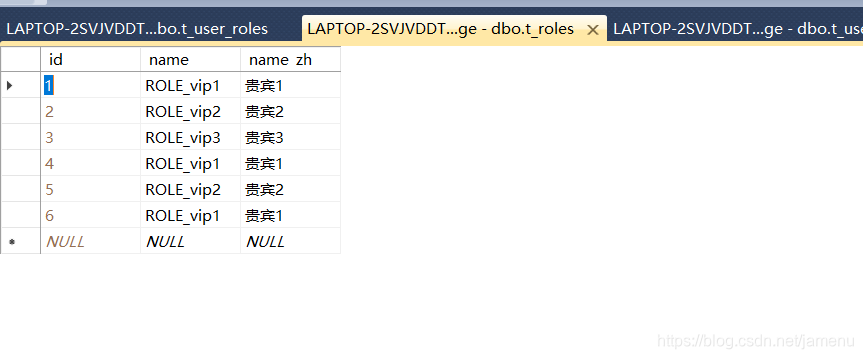
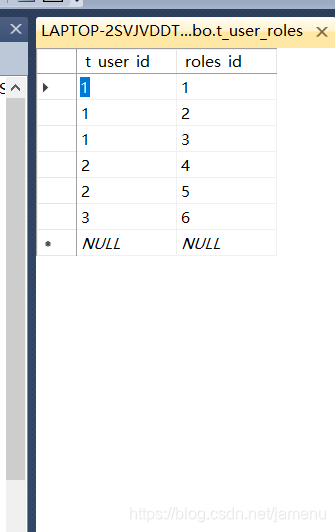
在测试类中添加并运行如下代码,在数据库中留下记录
@SpringBootTest
class SpringsercuiryApplicationTests {
@Autowired
UserDao userDao;
BCryptPasswordEncoder encoder;
@Test
void contextLoads() {
encoder = new BCryptPasswordEncoder();
User user = new User();
List<Role> lihansrole = new ArrayList<>();
lihansrole.add(new Role("ROLE_vip1","贵宾1"));
lihansrole.add(new Role("ROLE_vip2","贵宾2"));
lihansrole.add(new Role("ROLE_vip3","贵宾3"));
user.setUsername("lihan");
user.setPassword(encoder.encode("wdnmd"));
user.setAccountNonExpired(true);
user.setAccountNonLocked(true);
user.setCredentialsNonExpired(true);
user.setEnabled(true);
user.setRoles(lihansrole);
userDao.save(user);
//分割线
User user1 = new User();
List<Role> usersrole = new ArrayList<>();
usersrole.add(new Role("ROLE_vip1","贵宾1"));
usersrole.add(new Role("ROLE_vip2","贵宾2"));
user1.setUsername("root");
user1.setPassword(encoder.encode("wdnmd"));
user1.setAccountNonExpired(true);
user1.setAccountNonLocked(true);
user1.setCredentialsNonExpired(true);
user1.setEnabled(true);
user1.setRoles(usersrole);
userDao.save(user1);
/分割线
User user2 = new User();
List<Role> user2srole = new ArrayList<>();
user2srole.add(new Role("ROLE_vip1","贵宾1"));
user2.setUsername("guest");
user2.setPassword(encoder.encode("wdnmd"));
user2.setAccountNonExpired(true);
user2.setAccountNonLocked(true);
user2.setCredentialsNonExpired(true);
user2.setEnabled(true);
user2.setRoles(user2srole);
userDao.save(user2);
}
}

最后写一个springsecurity配置类
@EnableWebSecurity
public class securityconfiger extends WebSecurityConfigurerAdapter {
@Autowired
UserService userService;
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception {
auth..userDetailsService(userService).passwordEncoder(new BCryptPasswordEncoder());
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http.authorizeRequests().antMatchers("/").permitAll()
.antMatchers("/index").permitAll()
.antMatchers("/vc.jpg").permitAll()
.antMatchers("/Login_page").permitAll()
.antMatchers("/level1/**").hasAnyRole("vip1")
.antMatchers("/level2/**").hasAnyRole("vip2")
.antMatchers("/level3/**").hasAnyRole("vip3");
http.formLogin().loginPage("/Login_page").loginProcessingUrl("/Login_page");
http.csrf().disable();
http.logout().logoutSuccessUrl("/");
}
}
完成后启动项目用不同的用户名密码登录,完成了认证和授权
(之后改了代码,加了验证码,自定义了认证逻辑,忘了截图了。。。。。)
下面自定义认证逻辑
1.添加一下kaptcha的maven依赖
<dependency>
<groupId>com.github.penggle</groupId>
<artifactId>kaptcha</artifactId>
<version>2.3.2</version>
</dependency>
2.定义一个生成验证码的Controller,并把正确的验证码存入Session之中
@RestController
public class VerifyCodeController {
@Autowired
Producer producer;
@GetMapping("/vc.jpg")
public void getVerifyCodeImage(HttpServletResponse resp, HttpSession session) throws IOException {
resp.setContentType("image/jpeg");
String code = producer.createText();
session.setAttribute("verifyCode",code);
BufferedImage image = producer.createImage(code);
try(ServletOutputStream out = resp.getOutputStream()){
ImageIO.write(image,"jpg",out);
}
}
@Bean
public Producer VerityDode(){
//配置一下验证码
Properties properties = new Properties();
properties.setProperty("kaptcha.image.width","150");
properties.setProperty("kaptcha.image.height","50");
properties.setProperty("kaptcha.textproducer.char.string","0123456789");
properties.setProperty("kaptcha.textproducer.char.length","4");
Config config = new Config(properties);
DefaultKaptcha defaultKaptcha = new DefaultKaptcha();
defaultKaptcha.setConfig(config);
return defaultKaptcha;
}
}
定义MyAuthenticationProvider继承DaoAuthenticationProvider
并重写additionalAuthenticationChecks()方法添加验证码的逻辑
public class MyAuthenticationProvider extends DaoAuthenticationProvider {
@Override
protected void additionalAuthenticationChecks(UserDetails userDetails, UsernamePasswordAuthenticationToken authentication) throws AuthenticationException {
HttpServletRequest req = ((ServletRequestAttributes)RequestContextHolder.getRequestAttributes()).getRequest();
String input_code = req.getParameter("code");
String verify = (String)req.getSession().getAttribute("verifyCode");
if(input_code==null||verify==null||!input_code.equals(verify)){
throw new AuthenticationServiceException("验证码错误");
}
super.additionalAuthenticationChecks(userDetails, authentication);
}
}
之后需要改动一下security配置类
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception {
auth.authenticationProvider(myAuthentication());
}
@Bean
MyAuthenticationProvider myAuthentication(){
MyAuthenticationProvider myAuthenticationProvider = new MyAuthenticationProvider();
myAuthenticationProvider.setPasswordEncoder(new BCryptPasswordEncoder());
myAuthenticationProvider.setUserDetailsService(userService);
return myAuthenticationProvider;
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http.authorizeRequests().antMatchers("/").permitAll()
.antMatchers("/index").permitAll()
.antMatchers("/vc.jpg").permitAll()
.antMatchers("/Login_page").permitAll()
.antMatchers("/level1/**").hasAnyRole("vip1")
.antMatchers("/level2/**").hasAnyRole("vip2")
.antMatchers("/level3/**").hasAnyRole("vip3");
http.formLogin().loginPage("/Login_page").loginProcessingUrl("/Login_page");
http.csrf().disable();
http.logout().logoutSuccessUrl("/");
}
}
再稍微改一下登录页就行了
<body>
<form th:action="@{/Login_page}" method="post">
<span style="color: aqua;font-size: 36px;text-align: center">登录表单</span><br>
<label>用户名:</label><input type="text" name="username" /><br>
<label>密码:</label><input type="password" name="password"/><br>
<label>验证码</label><input type="text" name="code">
<input type="submit" value="登录"/>
</form>
<div>
<img th:src="@{/vc.jpg}" style="width: 150px;height: 50px" />
</div>
再次启动项目
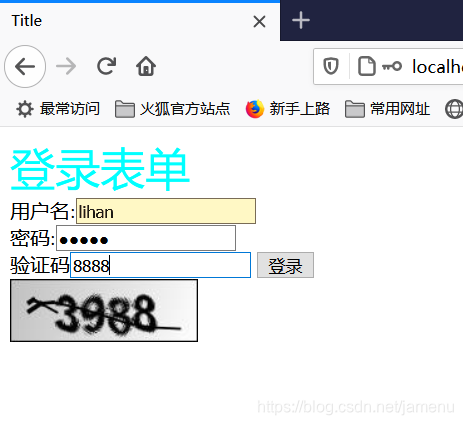
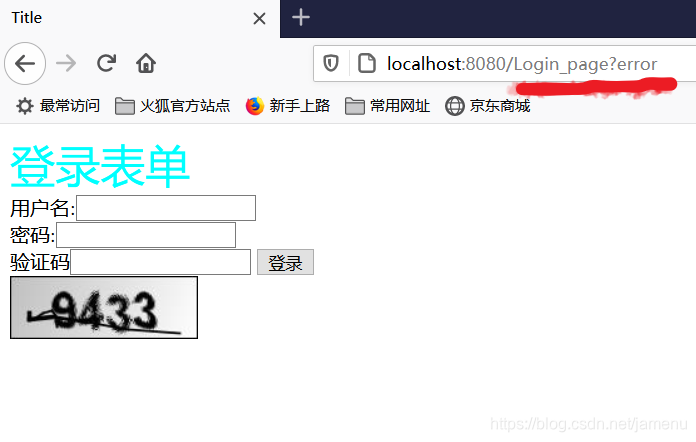
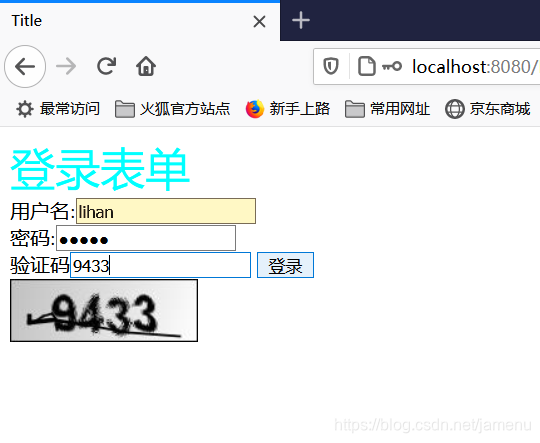
登录一下最低权限的账号

智能推荐
攻防世界_难度8_happy_puzzle_攻防世界困难模式攻略图文-程序员宅基地
文章浏览阅读645次。这个肯定是末尾的IDAT了,因为IDAT必须要满了才会开始一下个IDAT,这个明显就是末尾的IDAT了。,对应下面的create_head()代码。,对应下面的create_tail()代码。不要考虑爆破,我已经试了一下,太多情况了。题目来源:UNCTF。_攻防世界困难模式攻略图文
达梦数据库的导出(备份)、导入_达梦数据库导入导出-程序员宅基地
文章浏览阅读2.9k次,点赞3次,收藏10次。偶尔会用到,记录、分享。1. 数据库导出1.1 切换到dmdba用户su - dmdba1.2 进入达梦数据库安装路径的bin目录,执行导库操作 导出语句:./dexp cwy_init/[email protected]:5236 file=cwy_init.dmp log=cwy_init_exp.log 注释: cwy_init/init_123..._达梦数据库导入导出
js引入kindeditor富文本编辑器的使用_kindeditor.js-程序员宅基地
文章浏览阅读1.9k次。1. 在官网上下载KindEditor文件,可以删掉不需要要到的jsp,asp,asp.net和php文件夹。接着把文件夹放到项目文件目录下。2. 修改html文件,在页面引入js文件:<script type="text/javascript" src="./kindeditor/kindeditor-all.js"></script><script type="text/javascript" src="./kindeditor/lang/zh-CN.js"_kindeditor.js
STM32学习过程记录11——基于STM32G431CBU6硬件SPI+DMA的高效WS2812B控制方法-程序员宅基地
文章浏览阅读2.3k次,点赞6次,收藏14次。SPI的详情简介不必赘述。假设我们通过SPI发送0xAA,我们的数据线就会变为10101010,通过修改不同的内容,即可修改SPI中0和1的持续时间。比如0xF0即为前半周期为高电平,后半周期为低电平的状态。在SPI的通信模式中,CPHA配置会影响该实验,下图展示了不同采样位置的SPI时序图[1]。CPOL = 0,CPHA = 1:CLK空闲状态 = 低电平,数据在下降沿采样,并在上升沿移出CPOL = 0,CPHA = 0:CLK空闲状态 = 低电平,数据在上升沿采样,并在下降沿移出。_stm32g431cbu6
计算机网络-数据链路层_接收方收到链路层数据后,使用crc检验后,余数为0,说明链路层的传输时可靠传输-程序员宅基地
文章浏览阅读1.2k次,点赞2次,收藏8次。数据链路层习题自测问题1.数据链路(即逻辑链路)与链路(即物理链路)有何区别?“电路接通了”与”数据链路接通了”的区别何在?2.数据链路层中的链路控制包括哪些功能?试讨论数据链路层做成可靠的链路层有哪些优点和缺点。3.网络适配器的作用是什么?网络适配器工作在哪一层?4.数据链路层的三个基本问题(帧定界、透明传输和差错检测)为什么都必须加以解决?5.如果在数据链路层不进行帧定界,会发生什么问题?6.PPP协议的主要特点是什么?为什么PPP不使用帧的编号?PPP适用于什么情况?为什么PPP协议不_接收方收到链路层数据后,使用crc检验后,余数为0,说明链路层的传输时可靠传输
软件测试工程师移民加拿大_无证移民,未受过软件工程师的教育(第1部分)-程序员宅基地
文章浏览阅读587次。软件测试工程师移民加拿大 无证移民,未受过软件工程师的教育(第1部分) (Undocumented Immigrant With No Education to Software Engineer(Part 1))Before I start, I want you to please bear with me on the way I write, I have very little gen...
随便推点
Thinkpad X250 secure boot failed 启动失败问题解决_安装完系统提示secureboot failure-程序员宅基地
文章浏览阅读304次。Thinkpad X250笔记本电脑,装的是FreeBSD,进入BIOS修改虚拟化配置(其后可能是误设置了安全开机),保存退出后系统无法启动,显示:secure boot failed ,把自己惊出一身冷汗,因为这台笔记本刚好还没开始做备份.....根据错误提示,到bios里面去找相关配置,在Security里面找到了Secure Boot选项,发现果然被设置为Enabled,将其修改为Disabled ,再开机,终于正常启动了。_安装完系统提示secureboot failure
C++如何做字符串分割(5种方法)_c++ 字符串分割-程序员宅基地
文章浏览阅读10w+次,点赞93次,收藏352次。1、用strtok函数进行字符串分割原型: char *strtok(char *str, const char *delim);功能:分解字符串为一组字符串。参数说明:str为要分解的字符串,delim为分隔符字符串。返回值:从str开头开始的一个个被分割的串。当没有被分割的串时则返回NULL。其它:strtok函数线程不安全,可以使用strtok_r替代。示例://借助strtok实现split#include <string.h>#include <stdio.h&_c++ 字符串分割
2013第四届蓝桥杯 C/C++本科A组 真题答案解析_2013年第四届c a组蓝桥杯省赛真题解答-程序员宅基地
文章浏览阅读2.3k次。1 .高斯日记 大数学家高斯有个好习惯:无论如何都要记日记。他的日记有个与众不同的地方,他从不注明年月日,而是用一个整数代替,比如:4210后来人们知道,那个整数就是日期,它表示那一天是高斯出生后的第几天。这或许也是个好习惯,它时时刻刻提醒着主人:日子又过去一天,还有多少时光可以用于浪费呢?高斯出生于:1777年4月30日。在高斯发现的一个重要定理的日记_2013年第四届c a组蓝桥杯省赛真题解答
基于供需算法优化的核极限学习机(KELM)分类算法-程序员宅基地
文章浏览阅读851次,点赞17次,收藏22次。摘要:本文利用供需算法对核极限学习机(KELM)进行优化,并用于分类。
metasploitable2渗透测试_metasploitable2怎么进入-程序员宅基地
文章浏览阅读1.1k次。一、系统弱密码登录1、在kali上执行命令行telnet 192.168.26.1292、Login和password都输入msfadmin3、登录成功,进入系统4、测试如下:二、MySQL弱密码登录:1、在kali上执行mysql –h 192.168.26.129 –u root2、登录成功,进入MySQL系统3、测试效果:三、PostgreSQL弱密码登录1、在Kali上执行psql -h 192.168.26.129 –U post..._metasploitable2怎么进入
Python学习之路:从入门到精通的指南_python人工智能开发从入门到精通pdf-程序员宅基地
文章浏览阅读257次。本文将为初学者提供Python学习的详细指南,从Python的历史、基础语法和数据类型到面向对象编程、模块和库的使用。通过本文,您将能够掌握Python编程的核心概念,为今后的编程学习和实践打下坚实基础。_python人工智能开发从入门到精通pdf